The Current State Of The Tor Network September 2020
The Tor anonymity networks lets you browse the Internet anonymously, with traffic analysis resistance, thanks to the "wide diversity" of Tor relays. That "diversity" is in reality limited to a bunch of Tor relays crammed together in a few high-capacity data-centers Paris, Hanina (Germany), London, Amsterdam and Smithville, USA.
written by 윤채경 (Yoon Chae-kyung) 2020-09-24 - last edited 2020-09-27. © CC BY

The Tor Project, organization behind the Tor onion router anonymity software, sent us these lousy stickers. And a T-shirt.
The Tor anonymity software is interesting because it can, in theory, be used to create a traffic analysis resistant anonymity network. The torproject.org organization behind the software markets it as:
"Browse Privately. Explore Freely. Defend yourself against tracking and surveillance. Circumvent censorship."
We made this informative graphic explaining how Tor works in 2006:
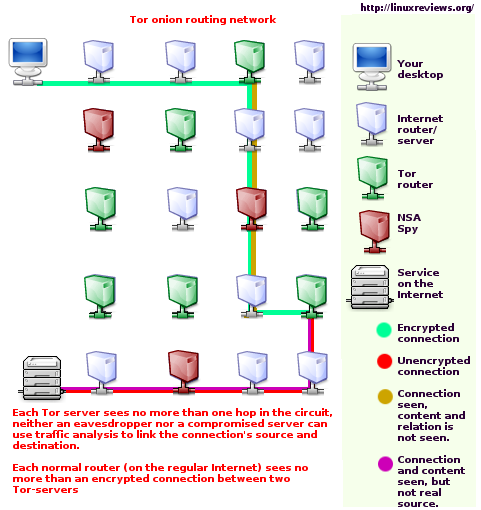
How Tor works explained by some drawing we made in 2006.
This is still, in principle, accurate. You can download the latest Tor Browser bundle and visit websites using the buggy Firefox ESR release in that bundle by going through a entry node, a middle relay and a exit node. You're fine even if the the adversary controls one of the three nodes you go through: Someone watching an exit node can't tell who you are, all they see is that there is traffic coming from some relay node between the entry node you are using and the exit node you are using. You are totally secure as long as the adversary can't see the entry node and the exit or the entry node and the website you are going to. That would be very hard if the Tor network consisted of tends of thousands of relays operated by tends of thousands of people all around the world. It would not be very hard if most of the nodes who make up the Tor network were crammed in next to each other in a few data-centers in central Europe.
The Actual State Of Affairs[edit]
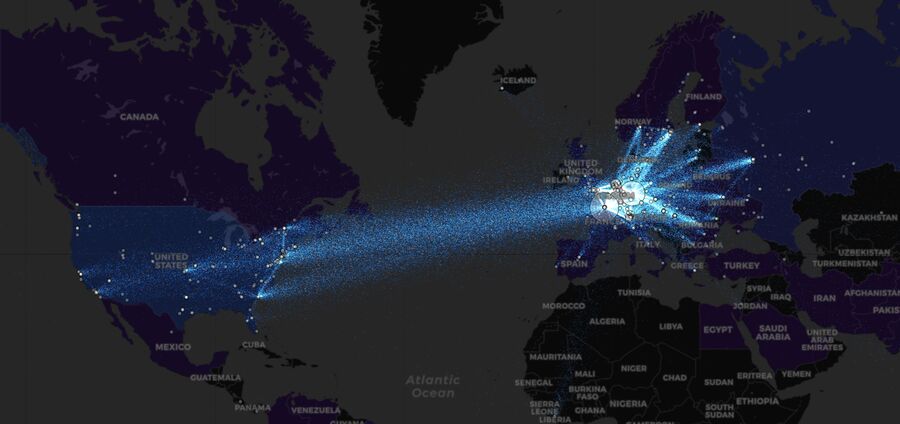
The Tor network's "diversity" September, 2020.
The vast majority of all Tor traffic jumps between a handful of locations in Europe. There are a few hot-spots in the US too but the American Tor surveillance capcity pales in comparison to the level the Europeans have.
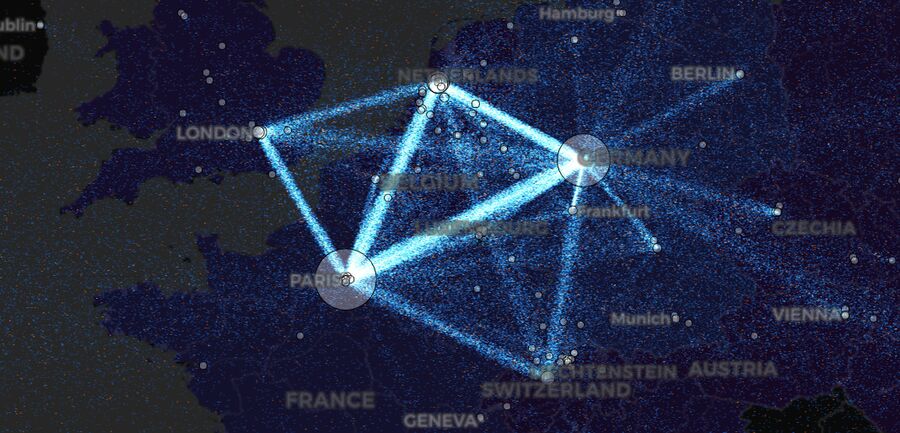
Tor nodes in Europe, September 2020.
There are 662 Tor nodes, most of them with unusually high bandwidth, in Paris. The Germans have 916 Tor nodes crammed together near Haina in the Hesse province. Amsterdam has 212 nodes and London has 141 nodes.
The Americans lack any similar capacity. They have 135 Tor nodes crammed together in a middle of no-where town called Smithville and another 104 in a rats-nest called "New York".
The only Russian presence in the Tor surveillance game is a mere 171 Tor relays crammed together in Moscow. That's slightly more than the Swedish National Defence Radio Establishment Corporation , a subsidiary of the Swedish Ministry of Defense, operates out of Stockholm. China simply isn't there.
Tor is typically described as a anonymity network ran by thousands random individuals who voluntarily run a Tor node in their basement using their average home Internet connection. That was mostly the case in the early years of it's existence. That changed around 2010. The situation today is that the vast majority of Tor nodes are running on dedicated high-bandwidth servers crammed together in a handful of European data-centers. The Tor network is a very centralized network, not a distributed network like it was meant to be.



Enable comment auto-refresher
Chaekyung