The Linux Kernel Had 3 Potential Root Access Vulnerabilities For 15 Years
Linux kernels prior to 5.11.4, 5.10.21, 5.4.103, 4.19.179, 4.14.224, 4.9.260 and 4.4.260 have three 15 year old vulnerabilities in the iSCSI subsystem that could potentially allow a hostile local user to gain root privileges. Most GNU/Linux distributions compile their kernels with ISCSI_TARGET=y so this could potentially be a problem with all of them, though RedHats distributions are the ones with an easy exploit-avenue.
written by 권유리 (Kwon Yu-ri) 2021-03-17 - last edited 2021-03-17. © CC BY
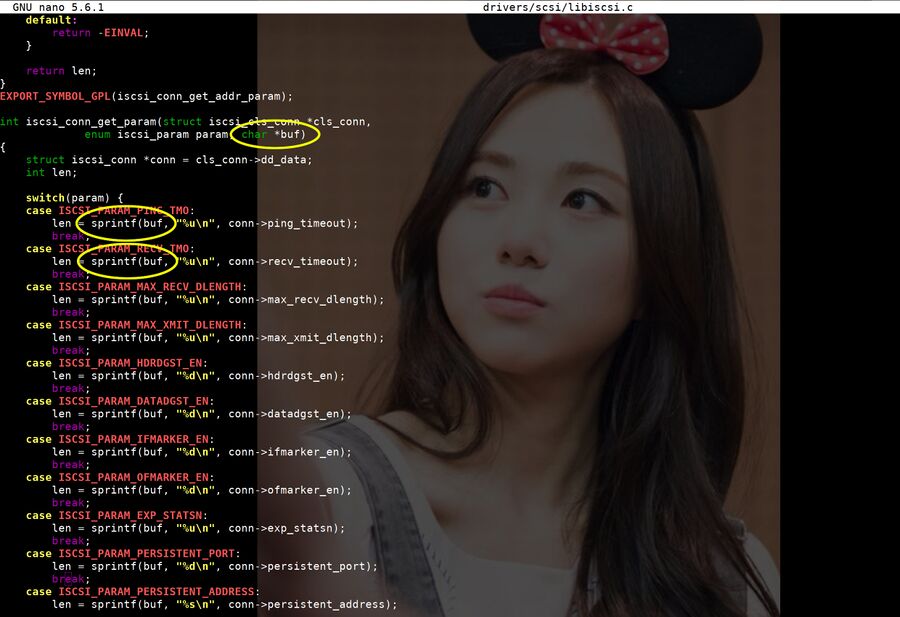
drivers/scsi/libiscsi.c from Linux 5.9.16. One does not simply use sprintf (buffer copy with no length) on a buffer without a length parameter.. yet that's what the Linux kernel did.
The cybersecurity firm GRIMM discovered three potentially dangerous bugs in the Linux kernels iSCSI subsystem in February. Those bugs had been present in the Linux kernel for 15 years before GRIMM discovered them and notified the kernel developers on February 17th, 2021. Mainline kernel patches became available on March 7th and all the current stable and longterm kernels have these patches.
GRIMM has developed a proof-of-concept Local Privilege Escalation (LPE) exploit using one of the tree vulnerabilities known as CVE-2021-27363, CVE-2021-27364 CVE-2021-27364 and CVE-2021-27365. It works, given the right circumstances, but that does not mean most people running Linux need to panic and upgrade within the next few minutes.
Good Old iSCSI[edit]
iSCSI is a network extension of the good old SCSI (Small Computer System Interface) data transport higher-end servers used to connect devices in the 1980s and 90s. It is not very common today and that is probably why nobody has bothered to look closely at the Linux kernels iSCSI code in ages. There are those who still use it, but the chance of some random Linux desktop or server using it is near-zero. You would know if you're one of the ten people in the world who still use it.
The iSCSI kernel vulnerabilities will only work if two iSCSI kernel modules are loaded. iSCSI kernel modules are typically not loaded on systems that do not use it, but they can be without too much hassle thanks to the Linux kernels on-demand module loading and a package called rdma-core for managing RDMA (Remote Direct Memory Access). Many distributions install this package by default and there is a fair chance that you have it installed.
The Linux kernel will load the scsi_transport_iscsi kernel module automatically when a socket call that creates a NETLINK_ISCSI socket is performed. The Linux kernel shipped with RedHat and Fedora will also load the ib_iser module (RDMA transport module for iSCSI) automatically if a regular system user creates a NETLINK_RDMA socket. Debian and distributions based on it, like Ubuntu, will not. Creating a NETLINK_RDMA socket on RedHats distributions is easy if the rdma-core package is installed.
The three iSCSI vulnerabilities can be neutralized by blacklisting the iSCSI modules in /etc/modprobe.d/ (create a iscsi.blacklist with blacklist modulename entries) or by eradicating the rdma-core package, if it is installed, or by upgrading to a Linux kernel released after March 7th. Those using Debian and distributions based on it should be safe without lifting a finger, but those of you who are using Debian-based distributions may want to ensure that you are using an up-to-date kernel just to be on the safe side. The iSCSI kernel modules would be loaded on Debian-based distributions if they are configured to use or serve iSCSI storage devices.
A remote attacker would have to gain regular user access by other means in order to use these vulnerabilities to turn that regular user access into root access. They are, in other words, irrelevant if you have a single-user desktop or laptop running GNU/Linux.
You can read a rather long and detailed write-up in the GRIMM blog in a post titled New Old Bugs in the Linux Kernel if you want the intricate details of each of the 3 vulnerabilities.


Enable comment auto-refresher