Microsoft GitHub Tightens Rules On Security Research And Copyright Circumvention
Microsoft GitHub has published a announcement of new rules around security research, proof of concept exploits, "malware", "harmful content" and code that could be used to circumvent copyright restrictions. A wide range of general-purpose software could fall afoul of the updated censorship policy. The rules new rules will take effect on June 1st, 2021.
written by 林慧 (Wai Lin) 2021-05-01 - last edited 2021-05-01. © CC BY
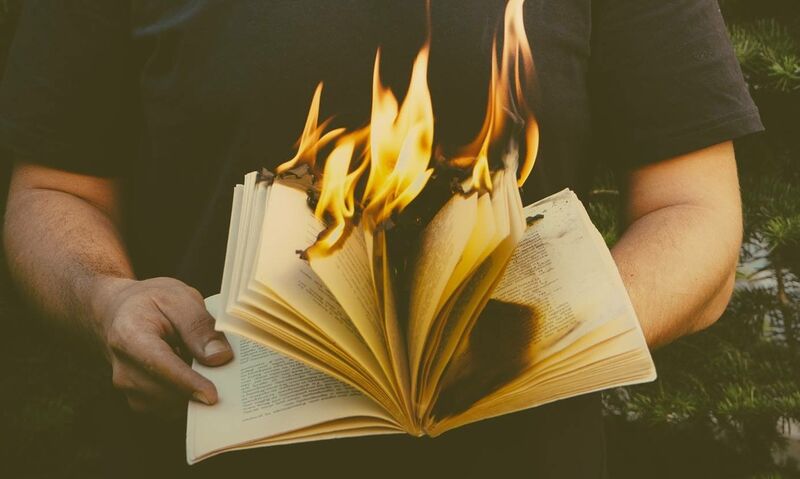
Censorship. It's always a bad idea.
Microsoft GitHub has published drafts for two new sets of rules that will affect all GitHub users come June 1st, 2021.
One deals with DMCA complaints about software that could be used to circumvent Digital Restrictions Management measures that restrict fair use of works protected by copyright. The draft for the new DMCA enforcement policy, titled "DMCA policy updates #395", refers to US Copyright law section 1201. That law lays out how American corporations can unjustly restrict how American citizens can use copies of copyrighted works they bought and paid for. GitHub is a subsidiary of the American Microsoft corporation, which is why GitHub is imposing this law on the entire world.
GitHub has been censoring a wide range of emulation tools and software for quite some time. The "new" DMCA will therefore not have any larger practical implications, it merely puts the existing unwritten policy in writing.
The other new rule-set GitHub is about to impose will have some slightly more tangible effects. GitHub has published a "draft" with new rules around security research titled "Exploits and malware policy updates #397". It comes as partly as a response to widespread criticism following Microsoft GitHub's removal of a exploit for the Microsoft Exchange server software. Critics pointed out that similar exploit code for competing products had not been taken down in the past.
The changes to the new upcoming "Open Exploits and malware policy updates" begin with a kind of sneaky change to all "Content Restrictions" in their overall acceptable use policies:
"Under no circumstances will Users upload, post, host, execute, or transmit any Content to any repositories that:"
is changed to
"Under no circumstances will Users upload, post, host, execute, or transmit any Content that:"
It makes sense to make all the rules apply to all of GitHub from GitHub's perspective. Why that general policy chance is made as a "Exploits and malware policy" change is anyone's guess.
The next policy change is specific to security-related code.
"Under no circumstances will Users upload, post, host, execute, or transmit any Content to any repositories that contains or installs malware or exploits that are in support of ongoing and active attacks that are causing harm"
This is a interestingly worded rule because there is a whole lot of different code that could be used to install other code from outside of GitHub. Common and on their own perfectly innocent pieces of software like curl and wget would be in violation of this policy if they are deemed to be used to fetch exploit code as part of some ongoing attack. Hashcat, everything with a http client and variety of general software could fall afoul of this policy.
The "Active malware or exploits" has also been updated with somewhat broad text clarifying that GitHub can not be used to "in support" of active attacks that "cause harm".
"We do not allow anyone to use our platform in support of active attacks that cause harm, such as using GitHub as a means to deliver malicious executables, or as attack infrastructure, for example by organizing denial of service attacks or managing command and control servers."
The Microsoft subsidiary is also adding a section where they acknowledge that some "research into vulnerabilities, malware or exploits" could educational value. Any such content must, when the new rules take effect:
"Clearly identify and describe any potentially harmful content in a disclaimer in the project’s README.md file."
and
"Provide a designated security contact through a SECURITY.md file in the repository."
Following those new rules will not be any guarantee against censorship of any vaguely security-related source code:
"GitHub may restrict content if we determine that it still poses a risk where we receive active abuse reports and maintainers are working toward resolution."
Microsoft GitHub has published a blog post titled "A call for feedback on our policies around exploits and malware" where it ask for "feedback" on their policy updates. The new policy will take effect on June 1st.
GitHub is just a very convenient web front end for the git version control system. There are several free software web front ends you can download and install on your own server if you object to any of GitHub's new or existing terms, and that is the only meaningful form of "feedback" you can give them. GitHub is not merely proposing new rules in order to have a discussion, it is simply announcing a new policy that will take effect as-is come June 1st, 2021.
--- The Russians are concerned about this development.


Enable comment auto-refresher
Anonymous (e4468cc0)
Permalink |
Anonymous (e4468cc0)
Anonymous (cd8e711c)
Permalink |
Anonymous (2dcc9bef)
Permalink |